-
Your First and Last Line of Defense

Oct 17, 2025The Hacker NewsArtificial Intelligence / Identity Security The danger isn’t that AI agents have bad days — it’s that they never do. They execute faithfully, even when what they’re executing is a mistake. A single misstep in logic or access can turn flawless automation into a flawless catastrophe. This isn’t some dystopian fantasy—it’s…
-
North Korean Hackers Combine BeaverTail and OtterCookie into Advanced JS Malware

The North Korean threat actor linked to the Contagious Interview campaign has been observed merging some of the functionality of two of its malware programs, indicating that the hacking group is actively refining its toolset. That’s according to new findings from Cisco Talos, which said recent campaigns undertaken by the hacking group have seen the…
-
New .NET CAPI Backdoor Targets Russian Auto and E-Commerce Firms via Phishing ZIPs

Oct 18, 2025Ravie LakshmananThreat Intelligence / Cybercrime Cybersecurity researchers have shed light on a new campaign that has likely targeted the Russian automobile and e-commerce sectors with a previously undocumented .NET malware dubbed CAPI Backdoor. According to Seqrite Labs, the attack chain involves distributing phishing emails containing a ZIP archive as a way to trigger…
-
Silver Fox Expands Winos 4.0 Attacks to Japan and Malaysia via HoldingHands RAT
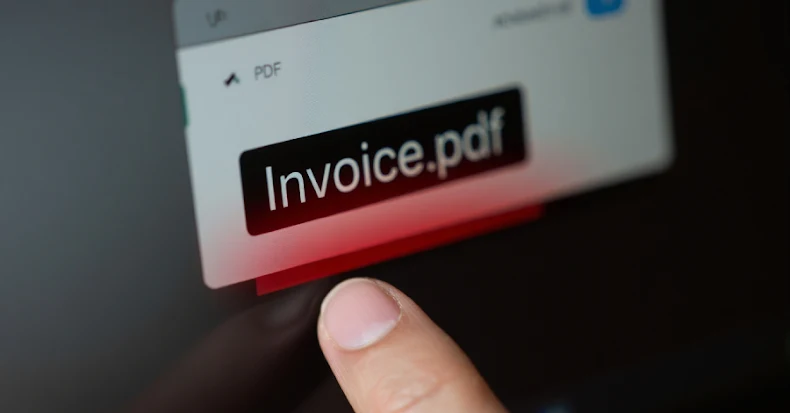
The threat actors behind a malware family known as Winos 4.0 (aka ValleyRAT) have expanded their targeting footprint from China and Taiwan to target Japan and Malaysia with another remote access trojan (RAT) tracked as HoldingHands RAT (aka Gh0stBins). “The campaign relied on phishing emails with PDFs that contained embedded malicious links,” Pei Han Liao,…
-
Europol Dismantles SIM Farm Network Powering 49 Million Fake Accounts Worldwide

Oct 19, 2025Ravie LakshmananSIM Swapping / Cryptocurrency Europol on Friday announced the disruption of a sophisticated cybercrime-as-a-service (CaaS) platform that operated a SIM farm and enabled its customers to carry out a broad spectrum of crimes ranging from phishing to investment fraud. The coordinated law enforcement effort, dubbed Operation SIMCARTEL, saw 26 searches carried out,…
-
MSS Claims NSA Used 42 Cyber Tools in Multi-Stage Attack on Beijing Time Systems

Oct 20, 2025Ravie LakshmananCyber Espionage / National Security China on Sunday accused the U.S. National Security Agency (NSA) of carrying out a “premeditated” cyber attack targeting the National Time Service Center (NTSC), as it described the U.S. as a “hacker empire” and the “greatest source of chaos in cyberspace.” The Ministry of State Security (MSS),…
-
131 Chrome Extensions Caught Hijacking WhatsApp Web for Massive Spam Campaign
Oct 20, 2025Ravie LakshmananBrowser Security / Malware Cybersecurity researchers have uncovered a coordinated campaign that leveraged 131 rebranded clones of a WhatsApp Web automation extension for Google Chrome to spam Brazilian users at scale. The 131 spamware extensions share the same codebase, design patterns, and infrastructure, according to supply chain security company Socket. The browser…
-
3 Reasons Why Copy/Paste Attacks Are Driving Security Breaches
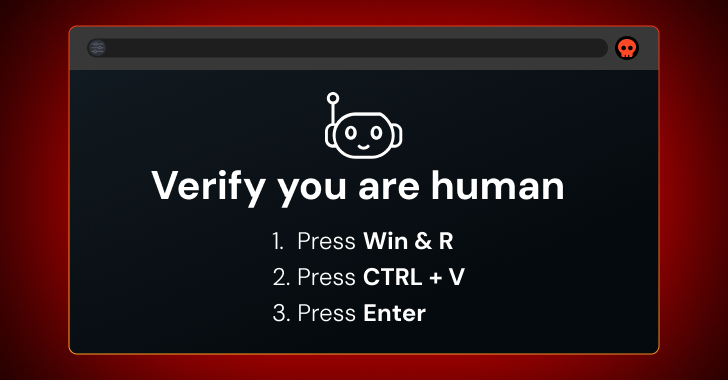
ClickFix, FileFix, fake CAPTCHA — whatever you call it, attacks where users interact with malicious scripts in their web browser are a fast-growing source of security breaches. ClickFix attacks prompt the user to solve some kind of problem or challenge in the browser — most commonly a CAPTCHA, but also things like fixing an error…
-
F5 Breached, Linux Rootkits, Pixnapping Attack, EtherHiding & More

It’s easy to think your defenses are solid — until you realize attackers have been inside them the whole time. The latest incidents show that long-term, silent breaches are becoming the norm. The best defense now isn’t just patching fast, but watching smarter and staying alert for what you don’t expect. Here’s a quick look…
-
Five New Exploited Bugs Land in CISA’s Catalog — Oracle and Microsoft Among Targets

Oct 20, 2025Ravie LakshmananThreat Intelligence / Data Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added five security flaws to its Known Exploited Vulnerabilities (KEV) Catalog, officially confirming a recently disclosed vulnerability impacting Oracle E-Business Suite (EBS) has been weaponized in real-world attacks. The security defect in question is CVE-2025-61884 (CVSS score:…
Search
About
Lorem Ipsum has been the industrys standard dummy text ever since the 1500s, when an unknown prmontserrat took a galley of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industrys standard dummy text ever since the 1500s, when an unknown prmontserrat took a galley of type and scrambled it to make a type specimen book. It has survived not only five centuries, but also the leap into electronic typesetting, remaining essentially unchanged.
Archive
Categories
Recent Posts
Tags
Gallery